Published on May 24, 2025
CVE-2024-30038: Full Analysis of Win32k Vulnerability and How to Fix It
In May 2024, Microsoft released information about a new, fairly serious security vulnerability, namely CVE-2024-30038. This vulnerability was found in the Win32k component in the Windows operating system and is categorized as an Elevation of Privilege Vulnerability. This means that if exploited, this gap could allow an attacker to elevate their access rights from a regular user to a system administrator.
With a fairly high level of severity, CVE-2024-30038 poses a serious threat to Windows users worldwide. This article will discuss in depth the details of the vulnerability, its impact, affected systems, and steps that need to be taken to address it.
What is CVE-2024-30038?
CVE-2024-30038 is a vulnerability that affects the Win32k component in the Windows operating system. Win32k is one of the main components that regulates the user interface, including operations such as window management, mouse and keyboard input, and other graphical elements.
This vulnerability allows a local attacker who already has limited access rights to exploit a weakness in Win32k and elevate his access rights to SYSTEM or Administrator. This means that the attacker can take full control of the system, run malicious code, and access sensitive data.
Vulnerability Type
CVE-2024-30038 is classified as Elevation of Privilege (EoP), which means that exploiting this vulnerability does not allow an attacker to directly enter the system, but provides the ability to elevate access rights after gaining a foothold on the system.
CVSS Score
Microsoft and the National Vulnerability Database (NVD) give a CVSS (Common Vulnerability Scoring System) score for CVE-2024-30038 of 7.8 (High).
- Attack Vector: Local (AV:L)
- Attack Complexity: Low (AC:L)
- Privileges Required: Low (PR:L)
- User Interaction: None (UI:N)
- Scope: Unchanged (S:U)
- Confidentiality: High (C:H)
- Integrity: High (I:H)
- Availability: High (A:H)
This score indicates that exploitation is relatively easy if an attacker already has local access to the system.
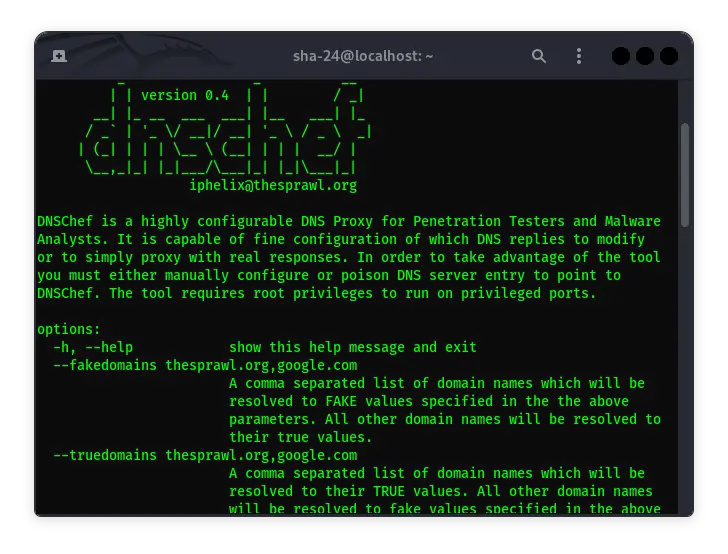
How Can CVE-2024-30038 Be Exploited?
This vulnerability exists due to an error in the way the Win32k component handles certain memory requests. An attacker could create a race condition or exploit an error in memory management to execute arbitrary code with elevated privileges.
Exploitation Scenarios
- An attacker gains access to the system with regular user credentials (e.g. through a phishing attack or credential theft).
- An attacker runs an exploit script that manipulates the Win32k component to gain access to kernel memory.
- If the exploit is successful, the attacker can escalate privileges to SYSTEM and take full control of the system.
- After gaining administrative access, the attacker can:
- Install malware.
- Delete or modify system files.
- Open network access for further attacks.
- Steal sensitive data.
Impact of CVE-2024-30038
This vulnerability has the potential to cause serious impact to individuals, businesses, and organizations. Some of the major impacts include:
- System Takeover
If the exploit is successful, the attacker can gain full control of the infected system. This could allow them to change the system configuration, add new user accounts, or plant a backdoor for future access.
- Data Theft
After gaining administrative access, attackers can copy or steal sensitive data such as:
- User login information
- Credit card data
- Confidential company documents
- Malware Distribution
Attackers can use administrative access to install malware on infected systems. This malware can then be used to:
- Create botnets
- Mine cryptocurrency
- Run ransomware
- Out of Service (DoS)
Attackers can make the system unstable or even cause repeated crashes to disrupt normal operations.
Affected Systems
The CVE-2024-30038 vulnerability has been reported to affect a variety of Windows versions, including:
- Windows 10 (version 1507 and later)
- Windows 11 (all versions prior to the May 2024 Update)
- Windows Server 2016, 2019, and 2022
Precautions and Mitigation Steps
To protect your system from exploiting CVE-2024-30038, the following steps are recommended:
- Update your system regularly
Microsoft has released a patch for CVE-2024-30038 in the May 2024 security updates. Make sure you update your operating system to the latest version via Windows Update.
- Limit User Access Rights
Use the principle of least privilege by only granting users the minimum access rights they need to perform their tasks. This will minimize the chances of an attacker gaining a foothold on the system.
- Use Endpoint Protection
Install updated security software (antivirus and antimalware) to detect and prevent attempts to exploit the vulnerability.
- Monitor System Activity
Monitor system activity logs for indications of suspicious or unusual activity that may be early signs of exploitation.
- Network Segmentation
Restrict access between systems by segmenting the network. If one system is infected, segmentation can prevent the spread of the exploit to other systems.
Recovery Process If Exploited
If the system has been infected by the CVE-2024-30038 exploit, here are the steps to perform recovery:
- Isolate System: Disconnect from the network to prevent further spread.
- Identify and Remove Malware: Perform a thorough scan using security software to remove malware or backdoors.
- Repair and Update System: Install the latest updates from Microsoft to close security holes.
- Change Credentials: Change all system passwords, including administrator accounts.
- Security Audit: Perform a thorough security audit to ensure that no other vulnerabilities remain.
Conclusion
CVE-2024-30038 is a serious vulnerability in the Win32k component that could allow an attacker to escalate privileges on a Windows system. With a high CVSS score and significant potential impact, it is important for users and system administrators to take immediate mitigation actions by updating systems and increasing security monitoring. By following the preventive measures above, you can protect your system from exploitation and maintain the security of your data and the integrity of your operating system.