Published on May 24, 2025
CVE-2024-30085: Privilege Escalation Vulnerability in Windows Cloud Files Mini Filter Driver
In 2024, a critical security vulnerability identified as CVE-2024-30085 was discovered in the Windows operating system. This vulnerability allows attackers to escalate their privileges to the SYSTEM level, meaning they can take full control of the infected system. The issue is located in the Windows Cloud Files Mini Filter Driver (cldflt.sys) component, which is used in cloud-based file operations, such as OneDrive and other storage services.
This vulnerability has attracted the attention of security researchers due to its potentially high impact, especially in corporate environments and systems that are widely used by individual users. This article will discuss CVE-2024-30085 in depth, starting from the technical background, exploitation mechanism, impact, to mitigation steps that can be taken to prevent attacks.
What is CVE-2024-30085?
CVE-2024-30085 is a vulnerability in the Windows Cloud Files Mini Filter driver (cldflt.sys) that allows a local attacker to perform privilege escalation to the highest level on the system, SYSTEM. If an attacker successfully exploits this vulnerability, they could:
- Execute malicious code with full administrative privileges.
- Modify or delete system files.
- Install additional programs without user permission.
- Create new user accounts with administrative privileges.
The vulnerability is due to insufficient data validation in the handling of reparse points in file operations. Reparse points are a feature of the NTFS file system that allows file operations to be redirected to a different location or mechanism, for example for cloud synchronization or symbolic link (symlink) purposes.
Technical Background
Cloud Files Mini Filter Driver (cldflt.sys) is a Windows driver used to manage files in cloud storage environments, such as OneDrive or SharePoint . This driver allows users to access cloud files without having to download the entire contents first.
How Reparse Points Work
- Reparse points are a mechanism in the NTFS file system that allows files or directories to be associated with additional metadata.
- When a user or application accesses a file that has a reparse point, the system forwards the operation to the appropriate handler, such as OneDrive or another cloud service.
- If data validation at the reparse point is inadequate, an attacker could manipulate this metadata to write to kernel memory or modify the structure of system objects.
Issues in CVE-2024-30085
The root issue in CVE-2024-30085 is inadequate input data validation in the cldflt.sys driver.
- An attacker could craft a custom reparse point that triggers a buffer overflow in the kernel memory heap.
- This buffer overflow allows an attacker to overwrite data structures in memory and execute malicious code with kernel privileges.
- The attacker can then manipulate objects in kernel memory to escalate privileges up to the SYSTEM level.
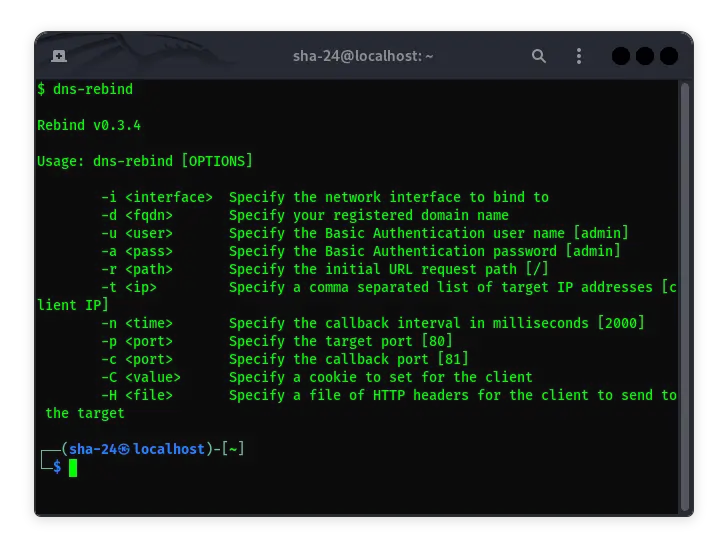
Exploitation Mechanism
The following are the technical steps that allow exploitation of CVE-2024-30085:
- Creating a Custom Reparse Point
- The attacker creates a file or directory with a custom reparse point.
- The metadata on this reparse point is configured in such a way as to manipulate operations at the kernel level.
- Triggering a Buffer Overflow
- When the system attempts to process the reparse point, the
cldflt.sysdriver fails to properly validate the length of the data. - This causes an excess of data to be written to the heap buffer, which then overwrites adjacent kernel object structures.
- Controlling Kernel Objects
- By manipulating kernel objects, the attacker can gain references to critical data structures in the operating system.
- The attacker can forge security objects or manipulate the process handle table (ALPC) to escalate privileges.
- Elevate Access Rights to SYSTEM
- Once kernel control is gained, the attacker can elevate access rights from a regular user to SYSTEM.
- At this point, the attacker has full control over the system, including the ability to modify the system and install malicious software.
Impact and Risks
CVE-2024-30085 has a significant impact, especially on enterprise environments and network-connected systems. Some of the key risks include:
- Full System Takeover
- An attacker can gain full administrative access to an infected system.
- This includes the ability to delete system files, install additional software, and modify system configurations.
- Data Theft
- An attacker can access sensitive files, user credentials, and other personal information.
- The stolen data can be used for further attacks, such as phishing or social engineering.
- Malware Spread
- After gaining elevated privileges, an attacker can spread malware throughout the internal network.
- This includes ransomware, spyware, or trojans that can cause financial and reputational losses.
Affected Systems
This vulnerability has been confirmed to impact:
- Windows 11 version 23H2
- Windows Server versions that use the
cldflt.sysdriver
How to Protect Your System from CVE-2024-30085
To prevent exploitation of CVE-2024-30085, here are some recommended mitigation steps:
1. Install Security Updates
Microsoft has released security updates that address CVE-2024-30085 in the June 2024 Patch Tuesday.
- Update your system immediately via Windows Update or the Microsoft Update Catalog.
- After the updates are installed, the
cldflt.sysdriver will improve its data validation process to prevent buffer overflows.
2. Restrict User Access Rights
- Limit administrative privileges to only accounts that are absolutely necessary.
- Use accounts with limited privileges for day-to-day operations to reduce the risk of exploitation.
3. Disable Cloud Features When Not Needed
If cloud storage features such as OneDrive are not used, consider disabling them to reduce the attack vector.
4. Use Endpoint Protection
Use a security solution such as Gunakan solusi keamanan seperti Windows Defender or third-party security software to detect and block kernel-based exploits.
5. Audit and Monitor
- Actively monitor system and process activity to detect anomalies or exploit attempts.
- Use intrusion detection (IDS) and intrusion prevention (IPS) tools to block exploits in real-time.
Conclusion
CVE-2024-30085 is a critical vulnerability that allows an attacker to gain elevated privileges on a Windows system via a buffer overflow exploit in the cldflt.sys driver. By understanding the exploit mechanism and implementing appropriate mitigation measures, users and system administrators can protect their systems from potential attacks. Apply security updates promptly and follow security best practices to prevent the impact of this vulnerability.