Published on May 28, 2025
How to Use SearchSploit on Kali Linux: A Complete Guide for Beginners and Professionals
SearchSploit is one of the most useful tools in the world of cybersecurity, especially for penetration testers and ethical hackers. This tool allows users to search and access exploits stored in the Exploit Database (Exploit-DB) database offline directly from the Kali Linux terminal. With SearchSploit, you can find exploits relevant to the system, application, or service you are testing, without the need to be connected to the internet.
In this article, we will discuss in detail what SearchSploit is, how to install it, how to use it, and tips for maximizing its use in the penetration testing process.
What is SearchSploit?
SearchSploit is a command-line interface (CLI) for the Exploit Database (Exploit-DB) created and maintained by Offensive Security . Exploit-DB itself is a repository containing thousands of exploit codes for various operating systems, software, and services. With SearchSploit, you can search and access those exploits locally without having to connect to the internet.
Why is SearchSploit Important?
- Offline Access: No internet connection is required to search for exploits.
- Efficiency: Searching for exploits becomes faster because it uses a local database.
- Up-to-Date: SearchSploit’s database can be updated anytime to get the latest exploits.
- Compatibility: SearchSploit supports various exploit formats such as C , Python , Perl , PHP , and others.
How to Install SearchSploit on Kali Linux
Most Kali Linux distributions already have SearchSploit installed by default. However, if SearchSploit is not available or you want to update to the latest version, you can follow these steps:
1. Update System Packages
Before installing or updating SearchSploit, make sure your system is up to date with the following command:
sudo apt update && sudo apt upgrade -y
2. Install Exploit-DB
If SearchSploit is not installed, you can install it using the following command:
sudo apt install exploitdb
3. Verify Installation
After the installation is complete, make sure SearchSploit has been installed properly by running the command:
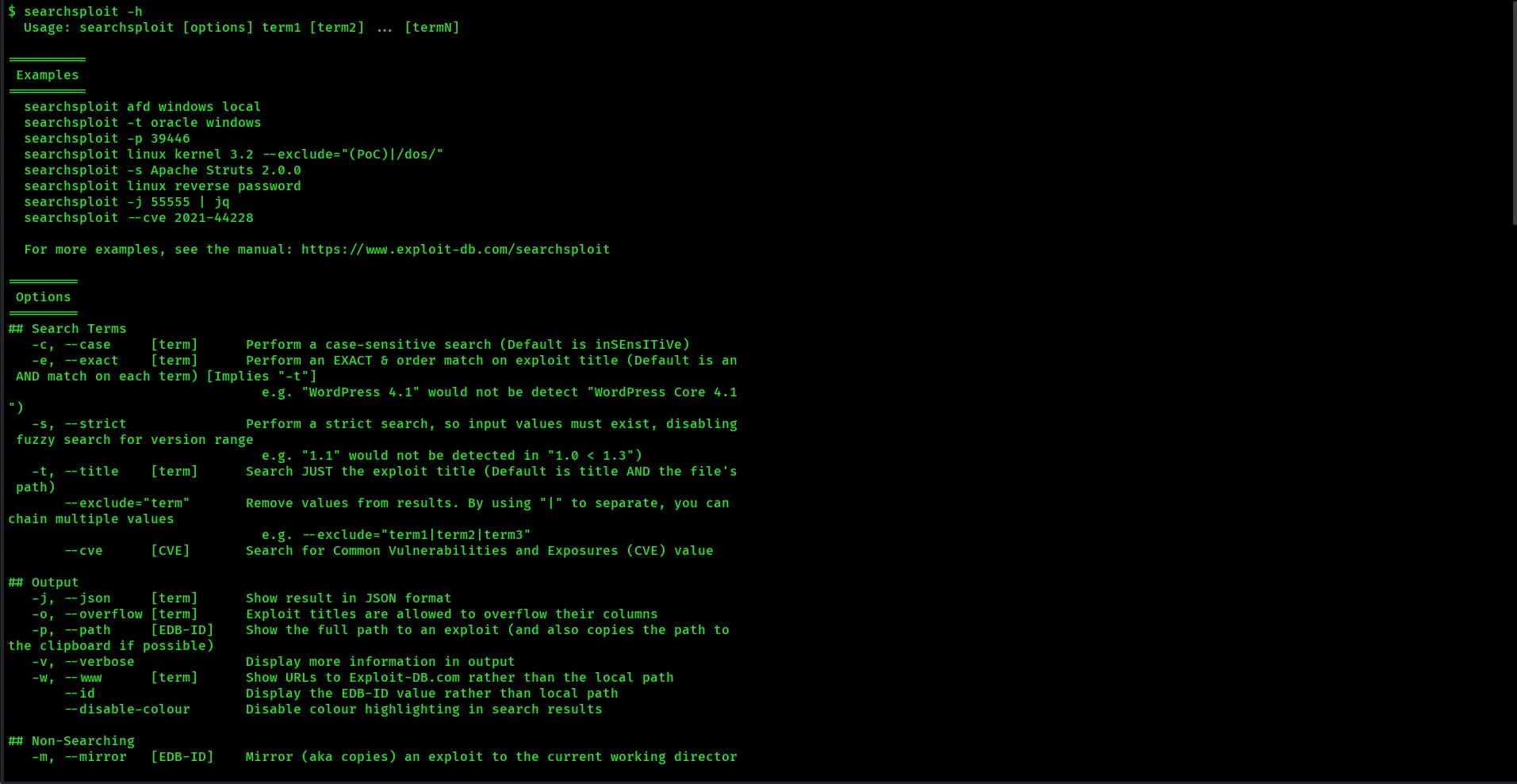
searchsploit -h
If the output appears in the form of a list of options and a usage guide, it means that the installation was successful.
How to Use SearchSploit on Kali Linux
Once SearchSploit is installed, you can start using it to search for the exploits you need. Here are some effective methods of using SearchSploit:
1. Searching for Exploits by Name or Version
To search for exploits that match the application name or version, use the following format:
searchsploit [application_name]
Example:
If you want to search for exploits for Apache, type:
searchsploit apache
The output will display a list of exploits related to Apache , complete with file paths and other details.
2. Filtering Search with Keywords
To narrow down the search results, you can add additional keywords:
searchsploit apache 2.4
This command will filter the search results to only Apache version 2.4.
3. Displaying Full Exploit Details
Once you find a matching exploit, you can display its details using the -x option:
searchsploit -x [file_location]
Example:
searchsploit -x exploits/linux/local/5092.c
This command will open and display the contents of the exploit code in the terminal.
4. Copying the Exploit to the Working Directory
If you want to use or modify the exploit, you can copy it to your working directory with the command:
searchsploit -m [file_location]
Example:
searchsploit -m exploits/linux/local/5092.c
This command will copy the file to your working directory.
5. Updating the SearchSploit Database
To keep the available exploits up to date, you can update the SearchSploit database with the command:
sudo searchsploit -u
This process will download the latest updates from Exploit-DB and update your local database.
Tips and Tricks for Using SearchSploit
Here are some tips to get the most out of SearchSploit:
Use Regex Options for More Specific Searches
SearchSploit supports searching with regex (regular expression). Example:
searchsploit 'apache.2\.4'
This command will search for exploits for Apache version 2.4 with a regex pattern.
Use a Cleaner Output Format
For a more readable display of the search results, use the -t option:
searchsploit -t apache
The output will be arranged in a more structured tabular format.
Integration with Metasploit
Many exploits found through SearchSploit can be directly imported into Metasploit. Once you find a suitable exploit, you can move it to the Metasploit directory:
cp /usr/share/exploitdb/exploits/linux/local/5092.c /root/.msf4/modules/exploits/
After that, run Metasploit and the exploit is ready to use.
SearchSploit Usage Case Study
For example, let’s try to find an exploit for OpenSSL :
- Search for OpenSSL Exploit
searchsploit openssl
- Copy the Exploit
searchsploit -m exploits/unix/remote/764.c
- Run and Test the Exploit
Open the copied file and follow the instructions to run the exploit.
Common Issues and Solutions
- SearchSploit Not Showing Search Results
Check your internet connection and run an update with the command sudo searchsploit -u.
- Exploit Not Working
Make sure the exploit is compatible with the target version and operating system.
- Exploit Not Found in Metasploit
Make sure the exploit file has been copied to the correct directory in Metasploit.
Conclusion
SearchSploit is a very useful tool in the penetration testing process because it provides fast and offline access to the world’s largest exploit database. By understanding how to search, copy, and run exploits, you can increase the efficiency and effectiveness of your security testing. Don’t forget to update the SearchSploit database regularly to always get the latest exploits.
By following this guide, you are now ready to use SearchSploit on Kali Linux professionally!