Published on May 24, 2025
ZoomEye Module: Complete Guide, Functions, and How to Use It
ZoomEye is a search engine designed specifically for reconnaissance of internet-connected devices, services, and open ports. Unlike search engines like Google or Bing that focus on searching web content, ZoomEye focuses on gathering information about devices and services active on the global network. ZoomEye is an invaluable tool for cybersecurity researchers, network administrators, and ethical hackers to identify potential security vulnerabilities and explore network infrastructure.
This article will discuss in detail about the ZoomEye Module, how to use it, its features, and its application in the world of cybersecurity. By reading this article, you will understand how ZoomEye works, how its module functions, and how to use it to strengthen your network security.
What is ZoomEye?
ZoomEye is a cybersecurity search engine created by Chinese cybersecurity company KnownSec. ZoomEye allows users to search for internet-connected devices by scanning IP addresses, services, and IoT (Internet of Things) devices. ZoomEye works by scanning public networks and storing the scan results in a database that can be accessed by users via a web interface or API.
Differences between ZoomEye and Conventional Search Engines
| Features | General Search Engines (Google, Bing) | ZoomEye |
|---|---|---|
| Search Focus | Content and web pages | Devices, services, and open ports |
| Target | General internet users | Cybersecurity researchers, ethical hackers, and network administrators |
| Information Access | Limited to page index results | Displays technical information about devices and networks |
How ZoomEye Works
- Port Scanning – ZoomEye scans IP addresses globally for open services and active ports.
- Service Fingerprinting – After finding an active service, ZoomEye will perform fingerprinting to identify the type of service, software version, and other technical information.
- Data Indexing – The scan results are then indexed in the ZoomEye database, which can be accessed via a search engine or API.
What is ZoomEye Module?
ZoomEye Module is a set of features or plugins in ZoomEye that allow users to perform advanced searches and gather more detailed information. This module provides the ability to filter search results, automate certain searches, and obtain additional data such as geolocation information, software versions, and detected vulnerabilities.
ZoomEye Module Main Functions
- Automated Scanning – Allows users to automate the scanning and searching process.
- Advanced Filtering – Provides the ability to filter search results based on certain criteria (eg: country, service type, port, and vulnerability).
- Data Extraction – Provides search results in JSON or CSV format for further analysis.
- Vulnerability Detection – Identifies potential security vulnerabilities in services or devices found.
- API Integration – Can be integrated with other cybersecurity tools such as Metasploit, Faraday, and Shodan.
How ZoomEye Module Works
ZoomEye Module allows users to perform structured searches using specific commands. Here is the basic workflow of ZoomEye Module:
- Login to ZoomEye Account
You need a ZoomEye account to access the module. Free accounts have search quota limitations, while premium accounts provide full access to the module’s features.
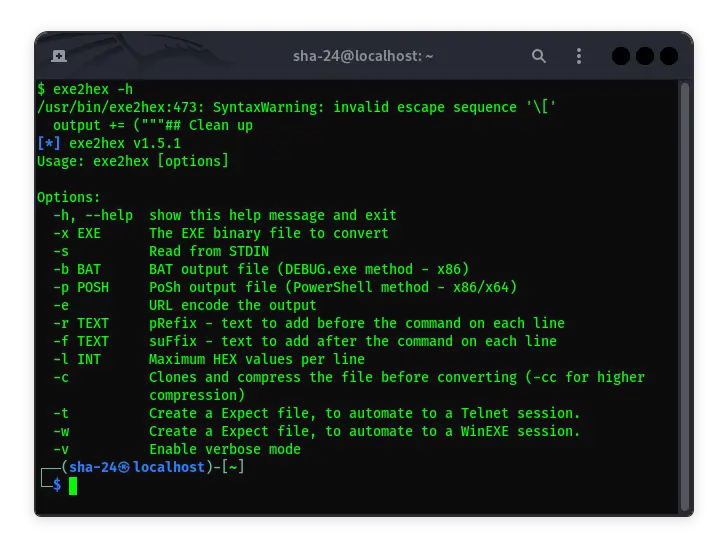
- Accessing ZoomEye Module
The module can be accessed through the web interface or through ZoomEye API. To activate the module through API, you need to get an API key from your ZoomEye account.
- Using Search Commands
Users can use search syntax to get more structured results.
Example Command:
zoomeye search "app:nginx country:US"
The above command will search for servers with NGINX applications located in the United States.
- Extracting and Analyzing Data
The search results can be extracted in JSON or CSV format for analysis using other tools.
ZoomEye Module Usage Example
1. Searching for Vulnerable Web Servers
To search for web servers running Apache that may have security vulnerabilities, you can use the following command:
zoomeye search "app:apache version:<2.4.10"
This command will list all Apache servers with versions lower than 2.4.10, which have potential security vulnerabilities.
2. Searching for Open IoT Devices
To find IoT devices that use the Telnet protocol and have open ports, you can use:
zoomeye search "service:telnet"
The results will display a list of IoT devices that are vulnerable because the Telnet port is open.
3. Analyzing Geolocation Information
To filter results based on geographic location, you can add a country filter:
zoomeye search "country:ID"
This command will display all devices connected to the internet in Indonesia.
ZoomEye Module Integration with Other Tools
1. Metasploit
ZoomEye can be integrated with Metasploit to identify targets before exploitation.
msf > use auxiliary/gather/zoomeye_search
2. Faraday
ZoomEye Module can also be integrated with Faraday to record search results in a vulnerability management system.
3. SearchSploit
Once you find a target, you can use SearchSploit to search for exploits that match the software or service versions found.
Security and Ethics of Using ZoomEye Module
Using ZoomEye Module for cybersecurity purposes requires high responsibility and ethics. Here are some principles to keep in mind:
Use for Security Research and Audit – Do not use ZoomEye for illegal activities such as hacking or illegal surveillance.
Respect Privacy – Do not access or interfere with systems discovered through ZoomEye.
Follow Local Laws and Regulations – Always ensure that your activities comply with applicable laws and regulations in your region.
ZoomEye Module Pros and Cons
Pros:
- Provides detailed technical data
- Supports APIs for automation and integration
- Covers extensive global scans
Cons:
- Limited search quota for free accounts
- Search results are sometimes not up-to-date
- Requires technical understanding to analyze results
Conclusion
ZoomEye Module is a very useful tool for cybersecurity researchers and network administrators to map devices and services active on public networks. With features such as advanced filtering, API integration, and automated analysis, ZoomEye Module is able to provide deep insights into potential security vulnerabilities and technical information about devices.
By understanding how ZoomEye Module works and following ethical principles in its use, you can use this tool to strengthen network security and increase resilience to cyberattacks.